1 min read
How Much Should Managed IT Services Cost in Cleveland (2026)
We talk to business owners across Northeast Ohio every week, and the number one frustration we hear isn't about broken printers or slow Wi-Fi. It's...

The phone rings at 4:00 PM on a Friday. It's your office manager, and they sound completely breathless. "I think I clicked a bad link," they say. Your stomach drops. Your heart races. In that single moment, a hundred terrifying questions flood your brain. Are the hackers already in? Is our customer data stolen? Are we going to be on the evening news?
If you're a business owner, you know this exact flavor of panic. It's a nightmare scenario, but you're definitely not alone in facing it. As a provider of local managed IT services Cleveland businesses rely on, we field this kind of frantic phone call all the time. Our goal today is to help you understand the real cost of human error, calm those fears, and give you a concrete plan to stop it from happening again.
Let's start with a harsh but necessary truth. According to the Verizon 2024 Data Breach Investigations Report, roughly 68 percent of all cybersecurity breaches involve a non-malicious human element. That means your biggest threat isn't a shadowy hacker breaking through your firewalls with sheer brute force. Your biggest threat is usually an exhausted employee trying to clear out their inbox before the weekend.
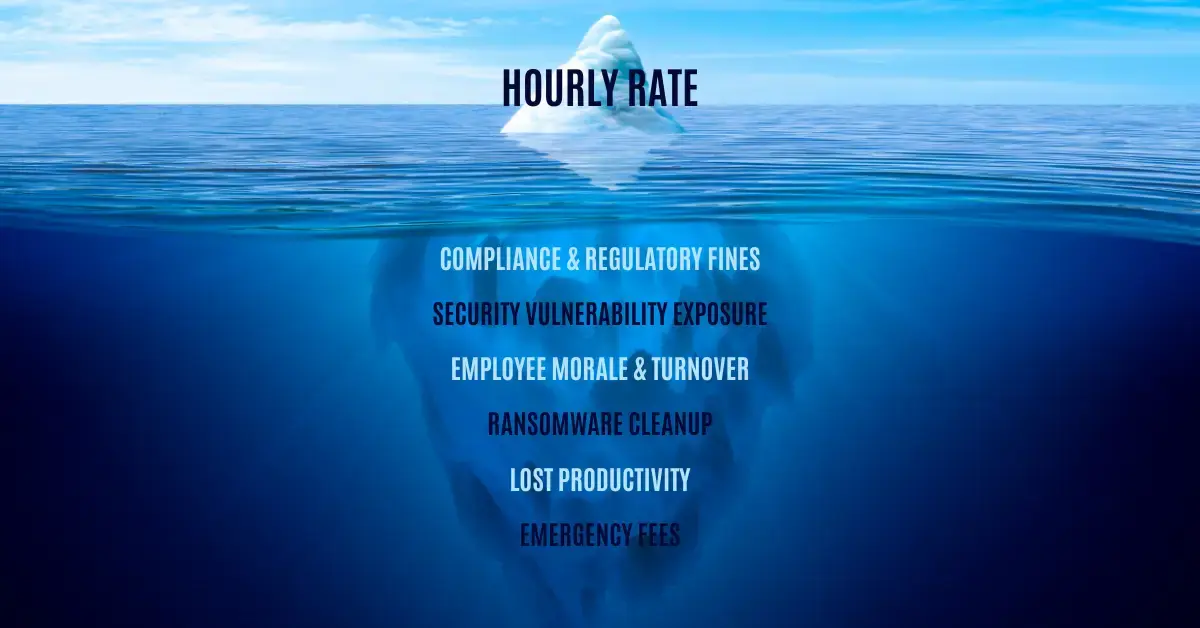
The real cost of human error goes far beyond paying a ransom to unlock your files, though that's certainly painful enough. The true financial bleed comes from the crushing weight of operational downtime. When your systems are locked, your team can't work, your clients can't reach you, and your revenue grinds to a complete halt. If you want to understand the foundational layers of protecting your business, you should explore our comprehensive guide to cybersecurity fundamentals.
For years, the IT industry told business owners that the silver bullet for human error was Security Awareness Training. The standard approach was to force employees into a stuffy conference room once a year, make them watch a dry PowerPoint presentation, and have them sign a piece of paper. Unsurprisingly, this approach failed miserably. It didn't change behavior; it just annoyed people.
Modern cyber threats require modern, engaging solutions. Today, we use simulated phishing campaigns and continuous learning platforms to keep teams sharp. But even then, not all training platforms are created equal. This brings us to a major debate in our industry: KnowBe4 vs. Huntress SAT.
When it comes to Security Awareness Training platforms, KnowBe4 and Huntress SAT are two of the biggest names in the conversation. Both platforms aim to solve the human error problem, but they take entirely different paths to get there.
I clearly remember rolling out KnowBe4 for a mid-sized client a few years ago. It's a massive, sprawling platform. I spent hours digging through their extensive library to build the campaign, but results were underwhelming. Employees felt tricked by the simulations and complained that the training videos were a boring chore. I watched users click through the modules as fast as humanly possible, retaining absolutely nothing.
In my opinion, KnowBe4 is an incredibly robust tool for enterprise compliance, but it often feels like a heavy administrative burden that misses the mark on actual human engagement. Huntress SAT, on the other hand, focuses on storytelling and gamification. Huntress uses recurring characters to teach lessons in a way that feels more like watching a short cartoon than taking a corporate quiz. When I tested it internally, I actually found myself laughing at the writing. The platform handles the heavy lifting, which frees up IT administrators to focus on other critical issues.
Your employees aren't your weakest link; they're your first line of defense. When you switch to a training platform that treats them like active defenders rather than liabilities, the entire culture of your organization shifts. People start confidently forwarding suspicious emails to the IT desk instead of quietly clicking on them out of curiosity.
Of course, training is only one piece of the puzzle. You also need the right technical safeguards in place to catch the things that inevitably slip through the cracks. For instance, if you're wondering about your endpoint protection, you might want to check out our hands-on review of Microsoft Defender for Business to see if it's enough.
Navigating the transition to a better security posture can feel overwhelming, but you don't have to do it alone. If you're tired of losing sleep over what your employees might be clicking, it might be time to rethink your entire IT strategy. To get started, you can learn everything you need to know about managed services and how a dedicated team can take this burden off your shoulders. And if you're worried about the headache of changing vendors, be sure to read about how to avoid the biggest traps when switching IT providers.
Stop waiting for the next bad click to dictate your Friday afternoon. Empower your team, implement the right tools, and take back control of your business.
%20Blog%20Post%20Feature%20Image%20WEBP.webp)
1 min read
We talk to business owners across Northeast Ohio every week, and the number one frustration we hear isn't about broken printers or slow Wi-Fi. It's...

1 min read
It’s one of the biggest crossroads a growing business faces. Things are scaling, the team is expanding, and the technology (which used to be an...
1 min read
The High Cost of Waiting for Something to Break We’ve all been there. You’re looking at your monthly expenses and wondering if that "IT maintenance"...